Forefront Unified Access Gateway is the next
generation edge access server from Microsoft. This section explores how
to set up Unified Access Gateway to access SharePoint sites using mobile
devices. You will need to complete these major steps to set up UAG for
SharePoint.
Set up SharePoint Alternate Access Mapping (AAM) for Cross Firewall Access.
Create an application portal trunk in UAG.
Set up the SharePoint application in UAG under the UAG trunk.
To access SharePoint sites
from mobile devices, the SharePoint devices have to be accessed and the
SharePoint Web application must be exposed to the mobile network. The
first step is to set up SharePoint Alternate Access Mapping (AAM) for
the Web application that is going to be exposed for mobile access. The
AAM allows mapping of the internal SharePoint sites to an URL accessible
from outside. The external URL is configured as one of the applications
in the UAG’s portal trunk.
1. Important Considerations
Before you delve
into the necessary configurations to publish SharePoint sites using
Unified Access Gateway, consider the following important aspects of
SharePoint and UAG.
1.1. Alternate Access Mappings
Alternate Access Mappings
or AAMs provide a mechanism for directing Web requests to the correct
Web applications. More importantly, AAMs provide users accessing the Web
application from the defined mapping with a consistent users’
experience by mapping all of the URLs that would normally appear to have
the address of the default Web application URL to the external URL. AAM
is a cornerstone in exposing internal SharePoint 2010 sites to Internet
and extranet zones. For example, the internal team sites portal for a
company that is accessed using http://teamsites/ can be accessed from the Internet using http://teamsites.contoso.com. You do this by configuring an AAM and specifying an Internet Zone URL for the Web application.
1.2. Public Host Names
Public
host names are the means by which each Web application is identified
when published through the UAG and accessed remotely. The public host
names assigned to the Web applications must share the UAG trunk’s parent
domain name. Table 1 shows examples of valid and invalid public host names.
Table 1. Valid and Invalid Public Host Names
| UAG TRUNK PUBLIC HOST NAME | TRUNK’S PARENT HOST NAME | VALID SHAREPOINT PUBLIC HOST NAME | INVALID SHAREPOINT PUBLIC HOST NAME |
|---|
| access.contoso.com | contoso.com | teams.contoso.com | teams.com |
| | | public.contoso.com | public.example.com |
2. Setting Up SharePoint for Cross-Firewall Access
Alternate Access Mapping allows
you to expose your SharePoint Web applications to different zones,
including an extranet, the Internet, and so on. To expose the SharePoint
sites to mobile devices, you must create an AAM that points to the
Internet zone for your Web application. The following steps explain how
to create the AAM for a mobile access scenario.
Open the Central Administration site.
Select Configure Alternate Access Mappings in the System Settings section.
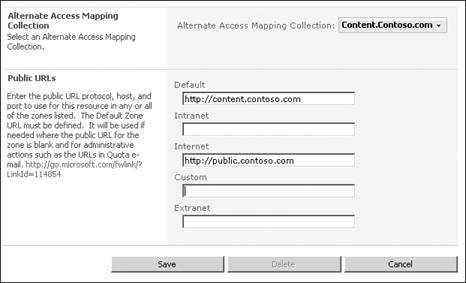
Click
Show All for Alternate Access Mapping Collection and then click Change
Alternate Access Mapping Collection. In the dialog box, select the Web
application you want to configure for mobile access.
Click the Edit Public URLs link.
Enter the URL (as shown in Figure 1) that you want to use for mobile access in the Internet zone.
Click Save to save your configurations.
Note:
The cross-firewall
configuration is ideal if you are planning to use Windows authentication
for Internet access to your SharePoint sites. If you are planning to
use a different authentication provider, you must extend the Web
application with the URL you want to use for the Internet Zone, and then
configure the authentication provider.
Now you have configured the SharePoint Web application for cross-firewall access. Next you need to set up the UAG
configuration that will enable access to this Web application from
Internet and mobile devices using the access gateway portal.
|
Some people are confused
about when to use Alternate Access Mappings and when to extend a Web
application to a zone. You might ask: Why do I have to extend my Web
application to another zone when I want to have IIS respond to a new
host header? Why can’t I simply add a URL for the existing Web
application zone?
The answer may be slightly counterintuitive, but it’s relatively easy to understand.
When you create a Web
application in SharePoint, the default Web application URL specified is
the only URL host header for which the corresponding Internet
Information Services (IIS) website will respond. If you need the
SharePoint WFEs and IIS to respond to a different URL host header, you
must extend the Web application to a different zone.
If you simply need to have the
URL links served by the Web application appear to be different from the
default URL host header, such as is the case with a secure access
gateway, you can accomplish this by simply adding a Public URL using
AAM.
This might be difficult to
comprehend initially, because when you want to have the website respond
to an additional host header in IIS, you simply add that host header to
the website, and it is there immediately. Logically the AAM interface
looks and feels a lot like this familiar IIS process, but deceivingly,
it’s not the same process, because an Alternate Access Mapping is just
that—a mapping, not an actual served URL.
Another difference is that
an extended Web application allows for different authentication
mechanisms and the serving of the same content across these
authentication mechanisms, in addition to being on different request
URLs. In the case of a secure access gateway, or any other reverse proxy
type configuration, the AAM is the perfect choice, because it maps the
user surfaced links and URLs in such a way that the requests are routed
to the proxy or gateway device, rather than the WEFs. Then the proxy or
gateway device sends that traffic to the WFEs by way of the default URL
Web application. AAMs make this type of off-boxed/proxy configuration
possible.
However, if you need to
create a simple firewall rule for external access to SharePoint data,
and the user requests will be processed directly by the WFEs, an
extended Web application provides you with both the mapping and the
additional host header response capabilities along with other benefits,
such as the authentication options.
|
3. Creating Application Portal Trunk in UAG
The steps involved in creating the application portal trunk are as follows.
Launch the Unified Access Gateway Management console.
Expand the Forefront Access Gateway node.
Right-click the HTTP Connections node and select New Trunk from the shortcut menu to open the New Trunk Wizard.
Click Next on the Welcome page of the wizard.
Select the Portal Trunk option and click Next to create a portal trunk, which in turn can publish SharePoint sites.
In the Setting The Trunk dialog box, specify the following details and click Next.
On the Step 4 – Authentication dialog box shown in Figure 2, specify the authentication server by clicking Add and then selecting the authentication server listed.
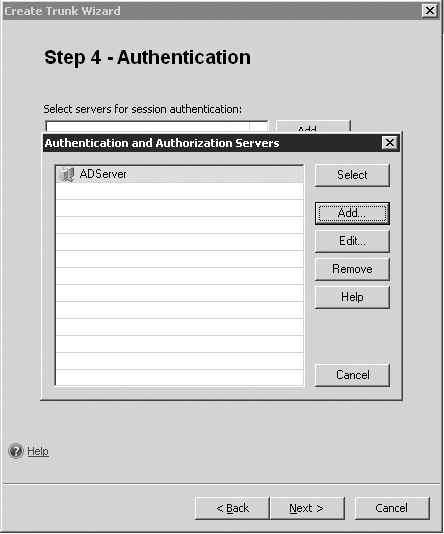
Click Select to confirm the selection and then click Next.
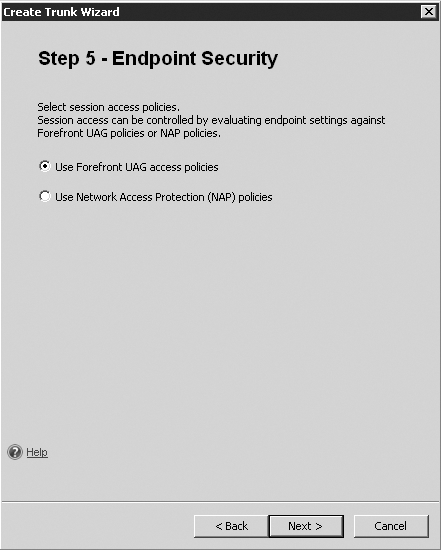
On the Step 5 – Endpoint Security dialog box shown in Figure 3, select the Use Forefront UAG Access Policies option and click Next.
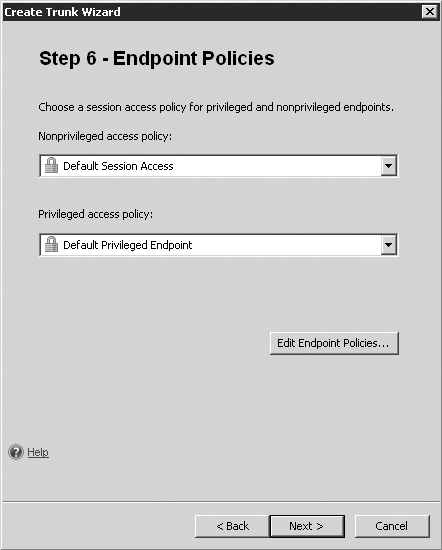
On the Step 6 – Endpoint Policies dialog box shown in Figure 4, accept the default Endpoint Policies and click Next.
On
the Completing The Create Trunk Wizard page, review your selections and
then click Finish to create the portal trunk. This portal trunk can be
used for creating application portals for SharePoint sites behind the firewall.